I think it is an elitist view based on an ideal world. A world where all companies have time and money to spend on information security and all consider it to be a top priority. For companies like banks, payment providers, governments or large service providers, information security is a critical success factor.
Our experience in the field shows that security is not top-priority for all companies. We see companies ignoring information security. Sometimes knowingly, but most of the times because they are just busy doing other stuff. Is that good? No. Do they have the time or experience to set up a proper information security program? No. Does enforcing or using a standard compliance framework (like PCI-DSS, HIPAA or GDPR) make them more secure? Definitely.
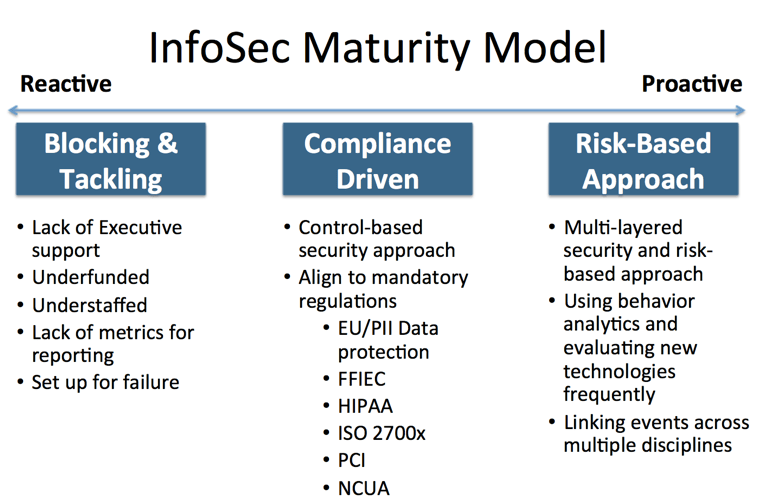
Move via compliance to security
The key difference between security and compliance is that security is inherently risk-based. It is there to protect the confidentiality, integrity and availability of the company’s assets. It protects by implementing controls against threats that cause risks the company is not willing to take. Compliance, on the other hand, is generally enforced on a company by external regulators to protect against a risk the regulator or industry is not willing to accept. This is a common set of accepted rules not taking company specifics or the fast-moving threat landscape into account.
For some companies, the minimum security requirements set by compliance frameworks are more than they currently have. Implementing a manageable and predefined set of rules sets the organization up for the first level of maturity and can be done in a relatively short time.
If you already have a solid security program, compliance should not be an issue. However, if you don’t have a security program, compliance framework will help you get one.
Source: Blue Lava
The risk-based approach works for companies that have reached a certain level of maturity. They have the experience, expertise and time and resources to do this. Also, they have a clear view of the risks they face.
We need to realize not all companies have the level of maturity that is required to implement the risk-based integral security approach. Not all companies will ever reach that level and for some, that is not required. Also going from 0 to 60 in 3 seconds will not be possible, so it makes sense to use the requirements in the compliance frameworks to get your organization up to a certain level.
Embrace compliance as part of your security
There are numerous examples of companies (also compliant companies) that get away with data breaches caused by careless security practices, leaving their customers with damages and risks. Compliance forces companies to think about their security practices, but to make it successful it has to be a program, not a project. Both compliance and security are a continuous process. Ticking the boxes is not difficult, keeping all boxes ticked every day of the year is.
Compliance is not something you should resist, but embrace every day. If everyone is serious about security, there would not be a need for compliance. Compliance helps to put information security on the agenda with management. It can help move organizations in the right direction towards security.
If compliance helps organizations to become more secure it is worth it. Most companies that are forced into compliance become more secure than they would have been without. Some organizations take security seriously because it is part of their DNA, because they see the added value, because they feel they owe it to their users or customers, or just because they feel it is the right thing to do. We applaud that. We feel the same. While we enjoy the work we do every day, we welcome the day compliance is obsolete. Until that day, we are ready to help, both with becoming compliant and becoming secure!
So take a compliance framework, embrace it, adopt it and use it to kick-start your security program.
Compliance is good, security is better. Don’t let perfect be the enemy of the good!
About the author:
Rogier Mars is a security professional with 20+ years of experience. During his consultancy work, he learns about new trends and views on information security. His views and expertise are appreciated widely in the security community.
