Retail Point-of-Sale (PoS) systems remain a top target for the financially motivated hacker. Theft of payment card data in large volume exists not only as its own segment within financial crime, but also serves to facilitate other even more harmful motives of today’s criminal elements.
To the businesses targeted by cyber criminals, the negative effects are far reaching with impact on brand reputation, consumer and investor confidence, and business growth strategies. With such a lucrative target as payment card data, adversary groups continue to adapt Tactics, Techniques, and Procedures (TTPs) in response to defenders’ change in security practices.
ShellTea and PoSlurp
A new malware campaign targeting retail PoS systems has been discovered. A targeted PoS intrusion focused on harvesting payment card information for exfiltration.
Analysis determined that the criminals are using advanced memory-resident techniques to maintain persistence and avoid detection. The malware likely required a significant amount of time and knowledge to create. We typically see techniques at this level by well-resourced, well-funded, motivated criminal organisations.
Methodology explained
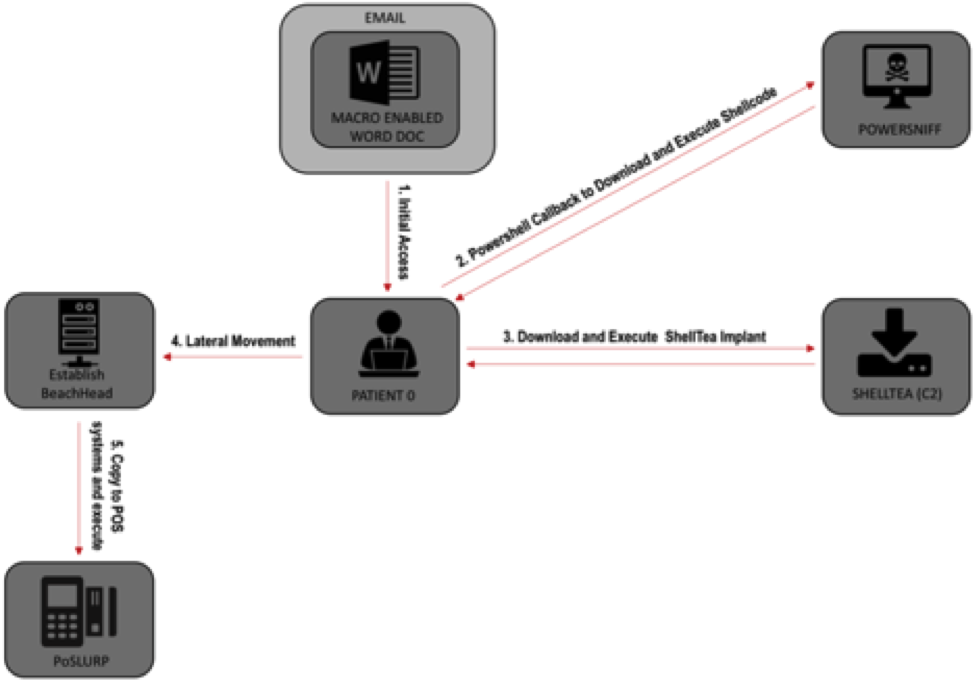
This on going campaign has targeted numerous organisations and their PoS systems. At a high-level, the methodology consists of the following steps:
Step 1: Spear Phishing email attack
Reconnaissance and targeting of a corporate individual with a spear phishing email attack employing an ActiveMIME document with a MS Office-enabled macro.
Step 2: Opening of the ActiveMIME document attachment and Initiating shell code download
Email recipient opens the ActiveMIME document attachment and clicks to enable content, executing a PowerShell command initiating a surreptitious shell code download.
Step 3: Dynamic Link Library (DLL) malware loaded into memory
A shell code blob encapsulating a Dynamic Link Library (DLL) malware is dropped in the system registry and loaded into memory, conducting basic enumeration and sandbox detection on the target. This malware appears to be an updated version of “PowerSniff”.
Step 4: Reconnaissance of target environment & additional instructions are send
The malware continues reconnaissance of the target environment and contact one of its five C2 domains with the results. If the environment meets the conditions the attacker is looking for, the attacked send additional instructions.
Step 5: ShellTea will be implanted
A second fillies implant will be implanted in another registry shell code blob. This implant (ShellTea) has not been previously observed or reported.
Step 6: Collecting of data from PoS endpoints
The attacker explores the network using compromised privileged credentials and establishes persistent staging servers for deploying malware and collecting data from PoS endpoints. Several staging servers are utilised by the attackers to spread the workload and provide redundancy to thwart defensive measures.
Step 7: PoSlurp is deployed to the PoS endpoints
An advanced PoS RAM scraping malware (named PoSlurp) is deployed to the PoS endpoints. PoSlurp directly injects memory-resident code into a privileged user mode process. This capability has not been previously reported. The attacker can specify which PoS processes should be monitored for payment card transactions.
Attack overview
6 tips on how to mitigate PoS malware attacks
1. Apply macro restrictions
This can prevent users from inadvertently running malicious Office macros to help address this common initial access vector.
2. Limit exposure privileged administrators
Follow best practices such as the PAW model, audit your credential risks, and require multi factor authentication for privileged users.
3. application whitelisting on PoS systems
Utilise Microsoft’s built-in AppLocker or one of many commercial solutions. Much like the previous mitigation recommendation, PoS systems should be highly standardised and have no software running or installed that is not part of required functionality.
4. Maintain a security monitoring program
Develop and maintain a robust security-monitoring program or contract an experienced security company.
5. Create Whitelists or Greylists
To ensure which domains and IP addresses that your organisation is allowed to reach via the network.
6. Prohibit communication between distinct segments
Such as PoS and Store networks, except for required ports and protocols. Using different credentials in each network will greatly delay, if not eliminate, the attacker’s ability to traverse the networks.
