by Gerdien van den Bosch | Nov 28, 2017 | Information security, Security tips
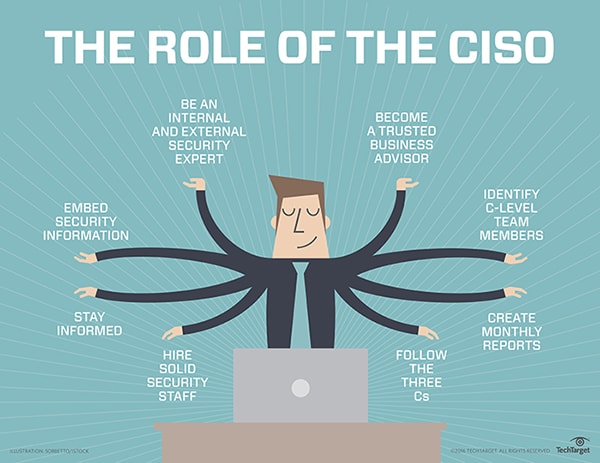
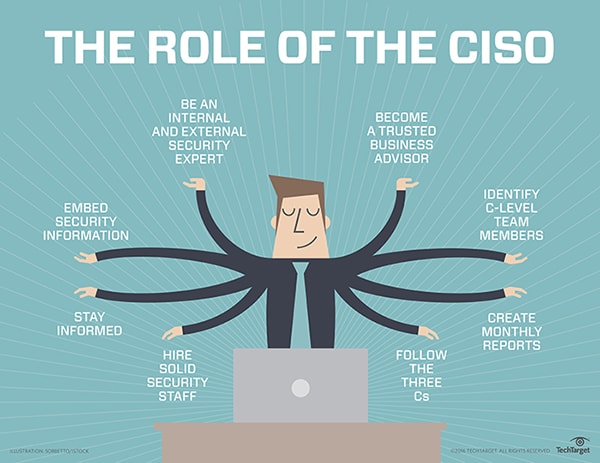
The role of the CISO (Chief Information Security Officer) is relatively new. While it is becoming increasingly accepted as a central role in managing the data and security measure, the profession continues to evolve. This is because information security isn’t just a...

by Gerdien van den Bosch | Sep 14, 2017 | Cybersecurity, Information security, PCI DSS
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) are the most commonly used encryption protocols and remains in widespread use today despite various security vulnerabilities exposed in the protocol in 2014. Both are used to authenticate to access to...

by Gerdien van den Bosch | Sep 7, 2017 | Information security
Penetration testing (or pen testing) – a legal attempt at gaining access to a protected computer system with the intention of identifying potential security loopholes in that system before cybercriminals do – is an integral part of information security. A pen...
by Gerdien van den Bosch | Sep 2, 2017 | Information security, Security tips
From the contents of emails to intellectual property, business plans, proprietary training documentation, and much more, most enterprises manage vast amounts of unstructured data containing valuable and sensitive information. The sheer volume of unstructured data...
by Gerdien van den Bosch | Aug 9, 2017 | Information security
With the Global Data Protection Regulation (GDPR) deadline fast approaching, many businesses remain entirely unprepared for the upcoming GDPR. Technology advisory firm Gartner predicts that by the end of 2018, more than half of companies still won’t be fully...
by Gerdien van den Bosch | Jul 13, 2017 | Information security
Misunderstanding these important tools can put your company at risk An often overlooked, but a very important process in the development of any Internet-facing service is testing it for vulnerabilities, knowing if those vulnerabilities are actually exploitable in your...